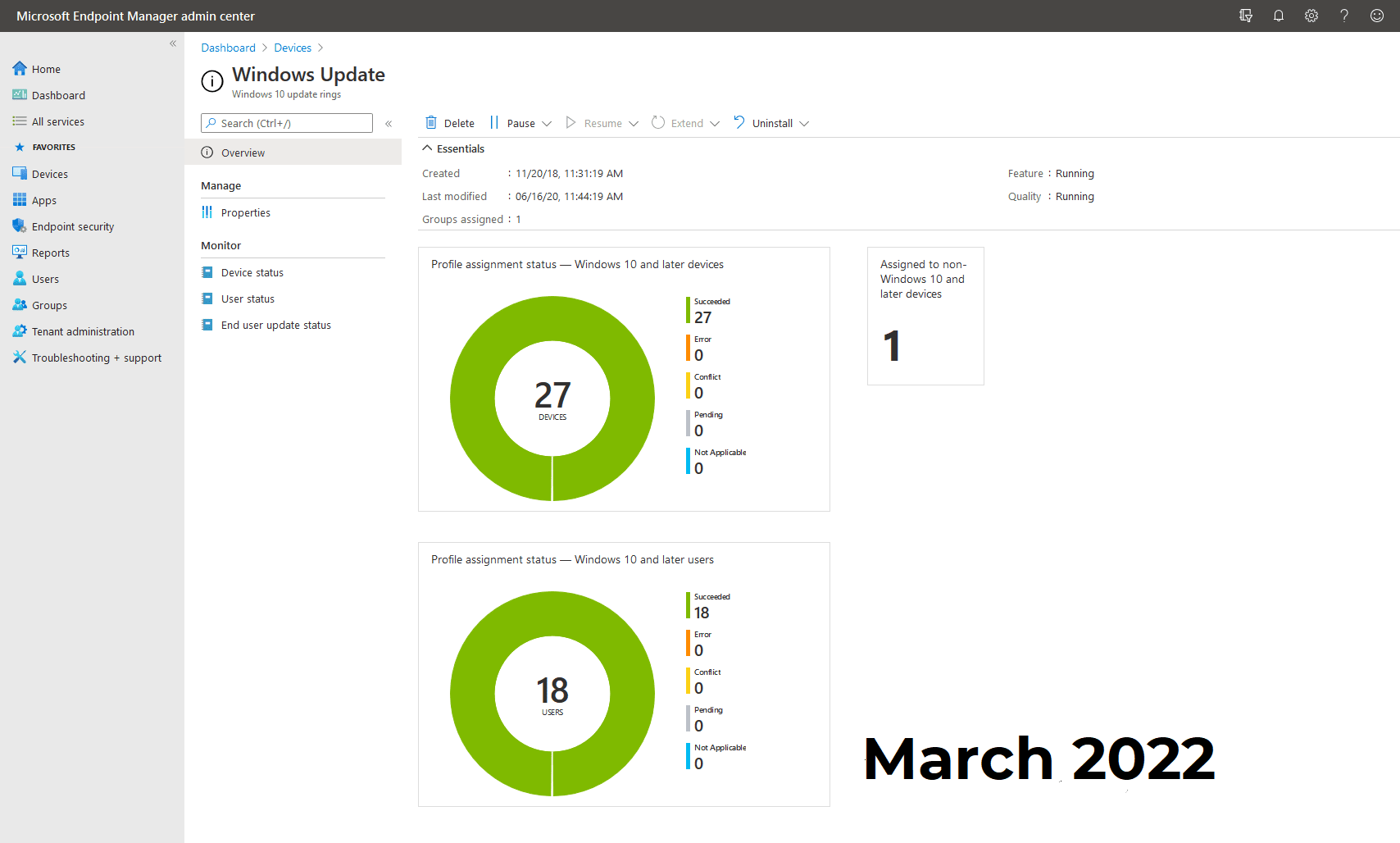
Foundation IT's March 2022 Patching Blog
It’s March, if the weather is anything to go by. It wouldn’t be March without a Microsoft Patch Tuesday to digest and handle. I’ve previously been asked whether I would recommend updating on Patch Tuesday or waiting, and in my opinion, I’d patch anything that is business critical or provides a resolution to crucial business functions – however I would always allow Microsoft updates to have a couple of weeks minimum. This allows updates to be pulled and re-released if there is an issue.
Dan Robinson
Technical Support Engineer
(dan.robinson@foundation-it.com)
What’s been published?
Microsoft fixes published: 92
Of which:
- Flagged as Critical: 3
- Flagged as Important: 68 (21 relate to Microsoft Edge)
- Flagged as Moderate: 0
- Flagged as Unknown: 21
Zero-Days Fixed: 3
The full breakdown for this month’s patch Tuesday by vulnerability type is:
- 25 Elevation of Privilege Vulnerabilities
- 3 Security Feature Bypass Vulnerabilities
- 29 Remote Code Execution Vulnerabilities
- 6 Information Disclosure Vulnerabilities
- 4 Denial of Service Vulnerabilities
- 3 Spoofing Vulnerabilities
- 21 Edge - Chromium Vulnerabilities
There have been 3 zero-day fixes this month and that relates to:
- CVE-2022-21990 - Remote Desktop Client Remote Code Execution Vulnerability
- CVE-2022-24459 - Windows Fax and Scan Service Elevation of Privilege Vulnerability
- CVE-2022-24512 - .NET and Visual Studio Remote Code Execution Vulnerability
There are 2 newly discovered zero-days to be aware of, but luckily not actively exploited yet.
- CVE-2022-24508 - Windows SMBv3 Client/Server Remote Code Execution Vulnerability
- CVE-2022-23277 - Microsoft Exchange Server Remote Code Execution Vulnerability
Worthy Mentions
- Google – Released March’s security updates.
- Cisco – Release numerous security updates.
- HP – Disclosed 16 UEFI firmware vulnerabilities.
Summary
Albeit fleeting, if you have Microsoft Exchange on your premise, pay some attention to CVE-2022-23277. Not currently exploited but may be one to watch in the coming weeks as these servers continually get targeted for attacks. CVE-2022-24508 has a workaround available, that you can find here. But as ever, keep an eye as an update will be released out of band for this one I would suspect. There were also a lot of Azure Site Recovery fixes released this month too, if you have made your way onto the ASR you’ll need to update to the latest version of the agent.
Happy Patching!
Additional Details
All details of this months patches can be downloaded here
We have also curated a free downloadable Patching Best Practice Guide.
About the Author: Dan Robinson
Dan is a Senior Technical resource within the managed service team. He looks after 1st line personnel and has a specialist skills with SCCM, Intune, Patching processes and general Infrastructure.