MS17-010 Windows SMB Remote Code Execution Vulnerability
- CVE-2017-0143
- CVE-2017-0144
- CVE-2017-0145
- CVE-2017-0146
- CVE-2017-0148
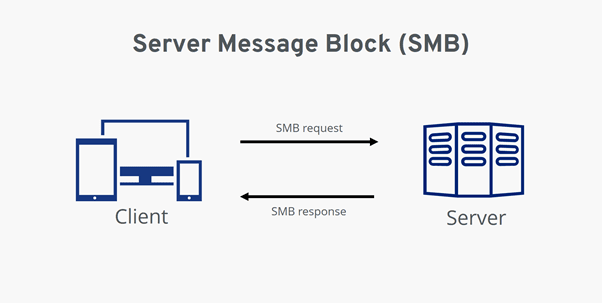
What is SMB? SMB or Server Message Block is a protocol for providing access to files, printers and other resources. It is part of every version of Windows and is very commonly enabled and allowed to pass through firewalls for legitimate reasons.
What is the vulnerability? Remote code execution vulnerabilities exist in the way that the Microsoft Server Message Block 1.0 (SMBv1) server handles certain requests. An attacker who successfully exploited the vulnerabilities could gain the ability to execute arbitrary code on the target server. Accordingly, the vulnerability is rated as critical.
What is the impact? Extremely high. At the time of writing the vulnerability is being widely exploited to execute ransomware. Several large organisations including Telefonica, FedEx and the NHS are suffering from being unable to access maliciously encrypted data. Media reports estimate 45,000 infected computers across 76 countries.
Am I affected? Microsoft released patches in March 2017. Systems that have not had security patches applied since then are likely vulnerable. All recent operating systems are affected. There is a list available here.
What conditions are required for this vulnerability to be exploited? You computer’s firewall must be configured to allow ‘File and Printer sharing’. Access to TCP/445 is enough for an attacker to exploit the vulnerability.
What should I do? Identify vulnerable machines and patch them immediately.
Foundation IT Managed Service customers will already have this patch applied in accordance with their contracted patching schedule and so no further action is required. Regardless, all customers will be contacted shortly with confirmation of systems that do not require patching and emergency remediation plans for any systems that have been unavailable for patching since the last cycle.

About the Author: Mike Starnes
Mike has worked in the IT Industry for over 20 years. If he's not talking technology, he'll be reading, playing football or trying to embarrass his daughters.