Foundation IT's January 2022 Patching Blog
Happy New Year to you and welcome to the Foundation IT Patching Blog. It is the start of a brand-new year and as you can imagine, it's straight back into the deep end when it comes to patching and vulnerabilities, and Microsoft has not held back for the first month of the year. Fortunately, nothing quite as substantial as Log4shell from December, but still some heavy hitters. Let us get into it.
Dan Robinson
Technical Support Engineer
(dan.robinson@foundation-it.com)
What’s been published:
Microsoft fixes published: 97
Of which:
- Flagged as Critical: 9
- Flagged as Important: 88
- Flagged as Moderate: 0
Zero Days Fixed: 6
Typically, I would cover the major fixes here but one of the major things to cover is that Microsoft had pulled the January Windows Server cumulative updates after finding critical bugs in them.
Some of the critical bugs included domain controllers going into a reboot cycle, Hyper-V not working and ReFS volume systems to become unavailable. This is an important thing to make note of, and a prime example of why you never patch your production systems on top of a patch Tuesday. There is nothing wrong with lag in this sense. I’ve always recommended a wait of at least a week before applying them to a nonproduction environment, then a week or so for that to bed in and then aim for your production. Even in this sense, patch your less critical devices first. Microsoft only has limited testing so can’t catch every scenario. The specific updates pulled are:
- KB5009624 – Windows Server 2012 R2
- KB5009557 – Windows Server 2019
- KB5009555 – Windows Server 2022
As soon as they disappeared they had reappeared with them showing once again in Windows Update, WSUS And the Microsoft Catalog. Microsoft however has confirmed they are now aware of the issues.
"After installing KB5009557 on domain controllers (DCs), affected versions of Windows Servers might restart unexpectedly. Note: On Windows Server 2016 and later, you are more likely to be affected when DCs are using Shadow Principals in Enhanced Security Admin Environment (ESAE) or environments with Privileged Identity Management (PIM),"
Here are those pesky zero-day vulnerabilities which have been resolved this month:
- CVE-2021-22947: HackerOne assigned CVE: An open-source Curl RCE allowing for Man-in-The-Middle (MiTM) attacks.
- CVE-2021-36976: MITRE assigned CVE: An open source Libarchive use-after-free bug leading to RCE.
- CVE-2022-21874: A local Windows Security Center API RCE vulnerability (CVSS 7.8).
- CVE-2022-21919: A Windows User Profile Service Elevation of Privilege security issue (CVSS 7.0), PoC exploit code recorded.
- CVE-2022-21839: Windows Event Tracing Discretionary Access Control List Denial-of-Service (DoS) (CVSS 6.1).
- CVE-2022-21836: Windows Certificate spoofing, PoC code recorded (CVSS 7.8).
None of the above vulnerabilities are known to be exploited.
Microsoft Edge received a vast amount of updates this month also, 24 in fact, which is the largest January Edge update push that is on record so far.
If you take anything away from this blog, plan your update delivery so that you do not get caught out by bad updates. Take time to plan and deliver your patching in a timely and safe fashion.
Worthy Mentions
- Adobe - January updates were released.
- Cisco - Released security updates for numerous products this month, including Cisco Prime Infrastructure and Cisco Common Services Platform Collector.
- SAP - released its January 2022 security updates.
- VMWare - released fixes for a code execution vulnerability in VMWare Workstation, Fusion, and ESXi.
Additional Details
All the patches can be found in the table below or alternatively downloaded here.
We have also curated a downloadable Patching Best Practice Guide.
About the Author: Dan Robinson
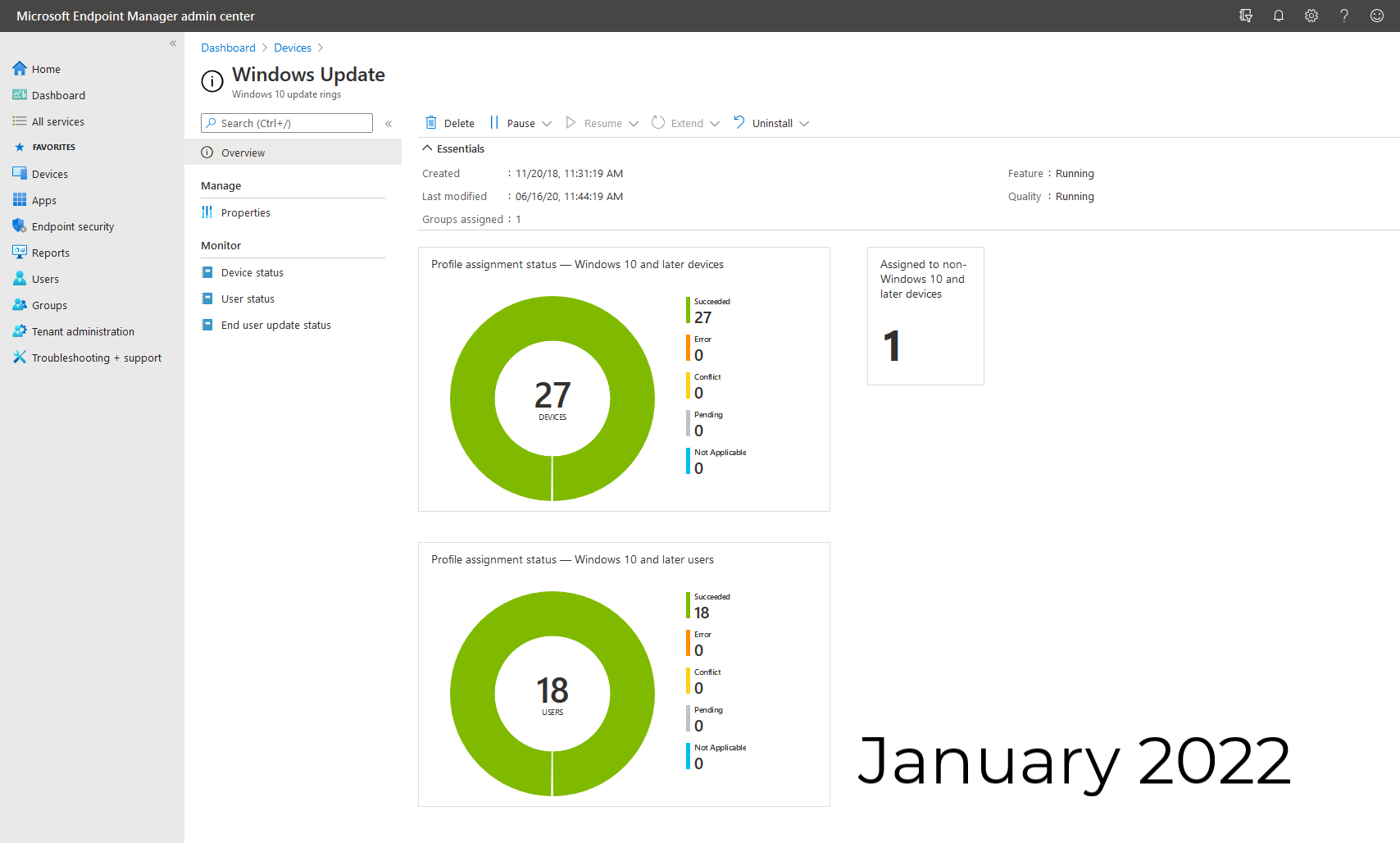
Dan is a Senior Technical resource within the managed service team. He looks after 1st line personnel and has a specialist skills with SCCM, Intune, Patching processes and general Infrastructure.