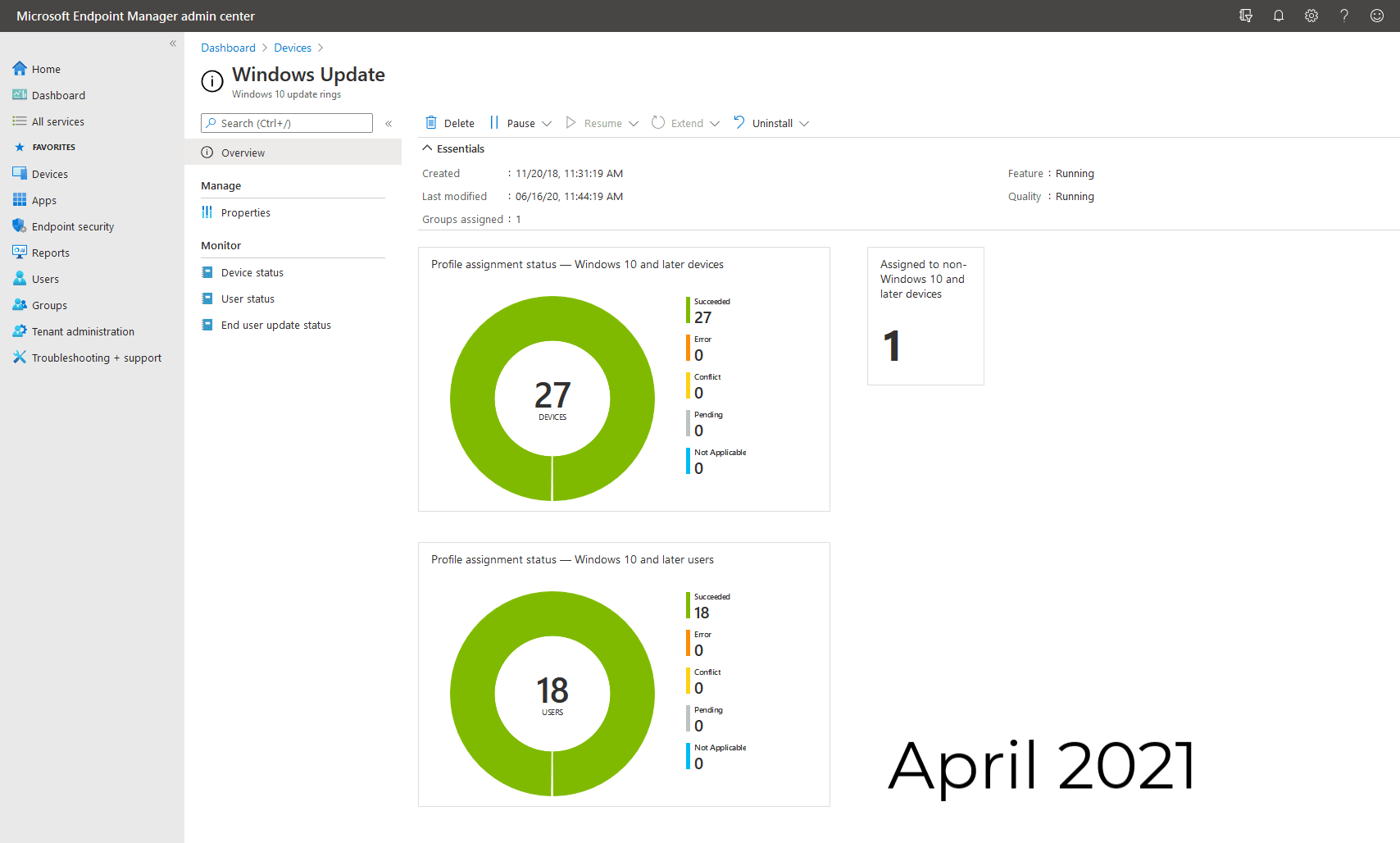
This week Microsoft released its security updates for April 2021, which has fixes for 108 vulnerabilities in Microsoft products. Every month we will post our vulnerability risk and tips around each patch released, to provide advice for IT professionals and businesses.
Out of the 108 patches; 19 are classed as critical and 89 are classed as important. These do not include the 6 Chromium Edge vulnerabilities released earlier this month. There were also 5 Zero-Days and more Critical Microsoft Exchange Vulnerabilities discovered this month:
-
CVE-2021-28310 - Win32k Elevation of Privilege Vulnerability.
-
CVE-2021-27091 - RPC Endpoint Mapper Service Elevation of Privilege Vulnerability.
-
CVE-2021-28312 - Windows NTFS Denial of Service Vulnerability.
-
CVE-2021-28458 - Azure ms-rest-nodeauth Library Elevation of Privilege Vulnerability.
-
CVE-2021-28437 - Windows Installer Information Disclosure Vulnerability - PolarBear.
Microsoft also released fixes for 4 Microsoft Exchange vulnerabilities not exploited in attacks:
-
CVE-2021-28480 - Microsoft Exchange Server Remote Code Execution Vulnerability
-
CVE-2021-28481 - Microsoft Exchange Server Remote Code Execution Vulnerability
-
CVE-2021-28482 - Microsoft Exchange Server Remote Code Execution Vulnerability
-
CVE-2021-28483 - Microsoft Exchange Server Remote Code Execution Vulnerability
Other Products:
Other companies who have released security updates this week:
- Adobe: released security updates for Adobe Creative Cloud Desktop, FrameMaker & Connect.
- Android: April security updates were released last week.
- Apple: released GarageBand security updates but has not provided details as to what has been fixed.
- Cisco: released security updates for numerous products.
- SAP: released it’s April 2021 security updates.
All the patches can be found in the table below or alternatively downloaded here.
We have also curated a downloadable Patching Best Practice Guide.
|
Category |
CVE IDs |
CVE Title |
Severity |
FIT Score & Tip |
|
Azure AD Web Sign-In |
CVE-2021-27092 |
Azure AD Web Sign-in Security Feature Bypass Vulnerability |
Important |
4/5 - This is an update for more modern OS (Windows 10 / Server 2019) which relates to a security vulnerability. It's worth patching this as it well. It forms part of the cumulative update for April 2021. |
|
Azure DevOps 2 |
CVE-2021-28459 CVE-2021-27067 |
Azure DevOps Server Spoofing Vulnerability Azure DevOps Server and Team Foundation Server Information Disclosure Vulnerability |
Important |
3/5 - If you use Azure DevOps Server, this is a separate patch that can be downloaded directly and applied. |
|
Azure Sphere 1 |
CVE-2021-28460 |
Azure Sphere Unsigned Code Execution Vulnerability |
Critical |
4/5 - As labelled Critical, pay this particular attention. This is a command-based update run directly on your Azure Sphere devices. |
|
Microsoft Edge (Chromium-based) 6 |
CVE-2021-21199 CVE-2021-21194 CVE-2021-21197 CVE-2021-21198 CVE-2021-21195 |
Chromium: CVE-2021-21199 Use Use after free in Aura Chromium: CVE-2021-21194 Use after free in screen capture Chromium: CVE-2021-21197 Heap buffer overflow in TabStrip Chromium: CVE-2021-21198 Out of bounds read in IPC Chromium: CVE-2021-21195 Use after free in V8 Chromium: CVE-2021-21196 Heap buffer overflow in TabStrip |
Unknown |
3/5 - This really depends on if your users utilise Microsoft Edge, If they don't use it - still patch it. As it's possible it has been left on the machine and could be accessed or used, thus allowing accessibility in via these CVEs. |
|
Microsoft Exchange Server 4 |
CVE-2021-28480 CVE-2021-28482 CVE-2021-28483 CVE-2021-28481 |
Microsoft Exchange Server Remote Code Execution Vulnerability |
Critical |
4/5 - After last months Exchange vulnerabilities, It would be worth continuing the trend this month and ensuring that Exchange is up to date. |
|
Microsoft Graphics Component 4 |
CVE-2021-28350 CVE-2021-28318 CVE-2021-28348 CVE-2021-28349 |
Windows GDI+ Remote Code Execution Vulnerability Windows GDI+ Information Disclosure Vulnerability |
Important |
3/5 - This forms part of monthly updates for Server O/S and also in monthly cumulative updates. |
|
Microsoft Internet Messaging API - 1 |
CVE-2021-27089 |
Microsoft Internet Messaging API Remote Code Execution Vulnerability |
Important |
3/5 - This forms part of monthly updates for Server O/S and also in monthly cumulative updates. |
|
Microsoft NTFS 2 |
CVE-2021-28312 CVE-2021-27096 |
Windows NTFS Denial of Service Vulnerability NTFS Elevation of Privilege Vulnerability |
Important |
4/5 - NTFS is the file system version for Windows, and with elevation of privilege this could compromise security. One to update when possible. |
|
Microsoft Office Excel 4 |
CVE-2021-28456 CVE-2021-28451 CVE-2021-28454 CVE-2021-28449 |
Microsoft Excel Information Disclosure Vulnerability Microsoft Excel Remote Code Execution Vulnerability Microsoft Excel Remote Code Execution Vulnerability Microsoft Office Remote Code Execution Vulnerability |
Important |
4/5 - Most, if not all users, will often use the Office suite, so it's recommended to update these as soon as possible. The main reason is your weakest vector is your end-users. |
|
Microsoft Office Outlook 1 |
CVE-2021-28452 |
Microsoft Outlook Memory Corruption Vulnerability |
Important |
4/5 - Most, if not all users, will often use the Office suite, so it's recommended to update these as soon as possible. The main reason is your weakest vector is your end-users. |
|
Microsoft Office SharePoint 1 |
CVE-2021-28450 |
Microsoft SharePoint Denial of Service Update |
Important |
4/5 - Most, if not all users, will often use the Office suite, so it's recommended to update these as soon as possible. The main reason is your weakest vector is your end-users. |
|
Microsoft Office Word 1 |
CVE-2021-28453 |
Microsoft Word Remote Code Execution Vulnerability |
Important |
4/5 - Most, if not all users, will often use the Office suite, so it's recommended to update these as soon as possible. The main reason is your weakest vector is your end-users. |
|
Microsoft Windows Codecs Library 5 |
CVE-2021-28464 CVE-2021-28466 CVE-2021-27079 CVE-2021-28468 CVE-2021-28317 |
VP9 Video Extensions Remote Code Execution Vulnerability Raw Image Extension Remote Code Execution Vulnerability Windows Media Photo Codec Information Disclosure Vulnerability Raw Image Extension Remote Code Execution Vulnerability Microsoft Windows Codecs Library Information Disclosure Vulnerability |
Important |
3/5 - It's worth reading into this one, as some of the updates come from the Microsoft Store (or Microsoft Store for Business). |
|
Microsoft Windows DNS 2 |
CVE-2021-28323 CVE-2021-28328 |
Windows DNS Information Disclosure Vulnerability |
Important |
3/5 - Most Windows networks will utilise Windows based DNS. I'd recommend updating this when possible. Once again this forms part of the monthly updates which are released. |
|
Microsoft Windows Speech |
CVE-2021-28351 CVE-2021-28436 CVE-2021-28347 |
Windows Speech Runtime Elevation of Privilege Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Open Source Software |
CVE-2021-28458 |
Azure ms-rest-nodeauth Library Elevation of Privilege Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Role: Hyper-V |
CVE-2021-28441 |
Windows Hyper-V Information Disclosure Vulnerability |
Important |
4/5 - Hyper-V is a pivotal part of any infrastructure (of course, only if you use it). Once again, this is in monthly patching, so applying the monthly updates should resolve this. Some of these are only applicable to later operating systems (Windows 10 / Server 2019 onwards) |
|
Visual Studio |
CVE-2021-27064 |
Visual Studio Installer Elevation of Privilege Vulnerability |
Important |
2/5 - Worth applying if you use Visual Studio, but worth noting this vulnerability is for the installer only. |
|
Visual Studio Code |
CVE-2021-28457 |
Visual Studio Code Remote Code Execution Vulnerability |
Important |
2/5 - Visual Studio Code is open source and this can be freely downloaded from the link that the CVE references. |
|
Visual Studio Code - GitHub Pull Requests and Issues Extension |
CVE-2021-28470 |
Visual Studio Code GitHub Pull Requests and Issues Extension Remote Code Execution Vulnerability |
Important |
2/5 - This is applicable if you use the reference extension only. You can download this from the CVE which is reference. |
|
Visual Studio Code - Kubernetes Tools |
CVE-2021-28448 |
Visual Studio Code Kubernetes Tools Remote Code Execution Vulnerability |
Important |
2/5 - This is applicable if you use the reference extension only. You can download this from the CVE which is reference. |
|
Visual Studio Code - Maven for Java Extension |
CVE-2021-28472 |
Visual Studio Code Maven for Java Extension Remote Code Execution Vulnerability |
Important |
2/5 - This is applicable if you use the reference extension only. You can download this from the CVE which is reference. |
|
Windows Application Compatibility Cache |
CVE-2021-28311 |
Windows Application Compatibility Cache Denial of Service Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Windows AppX Deployment Extensions |
CVE-2021-28326 |
Windows AppX Deployment Server Denial of Service Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Windows Console Driver |
CVE-2021-28438 |
Windows Console Driver Denial of Service Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Windows Diagnostic Hub |
CVE-2021-28313 |
Diagnostics Hub Standard Collector Service Elevation of Privilege Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Windows Early Launch Antimalware Driver |
CVE-2021-28447 |
Windows Early Launch Antimalware Driver Security Feature Bypass Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Windows ELAM |
CVE-2021-27094 |
Windows Early Launch Antimalware Driver Security Feature Bypass Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Windows Event Tracing |
CVE-2021-27088 |
Windows Event Tracing Elevation of Privilege Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Windows Installer |
CVE-2021-26413 |
Windows Installer Spoofing Vulnerability |
Important |
4/5 - Windows Installer is used for installing programs and also doing Windows Update. It's used more often than not, and utilised by the operating system in the background too. I'd recommend getting your monthly updates done when you can to resolve this. |
|
Windows Kernel |
CVE-2021-27093 |
Windows Kernel Information Disclosure Vulnerability |
Important |
4/5 - The Windows Kernel is the heart and brain of the OS, a bit like other operating systems - the Kernel is the core component of the functional operating system. This forms part of the monthly updates. |
|
Windows Media Player |
CVE-2021-28315 |
Windows Media Video Decoder Remote Code Execution Vulnerability |
Critical |
4/5 - Flagged as Critical by Microsoft, these fixes are within your monthly updates for April 2021. |
|
Windows Network File System |
CVE-2021-28445 |
Windows Network File System Remote Code Execution Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Windows Overlay Filter |
CVE-2021-26417 |
Windows Overlay Filter Information Disclosure Vulnerability |
Important |
3/5 - This is for more modern operating systems (Windows 10 and later server operating systems) but once again included within your monthly patches. |
|
Windows Portmapping |
CVE-2021-28446 |
Windows Portmapping Information Disclosure Vulnerability |
Important |
3/5 - This vulnerability is resolved within your normal routine monthly updates. |
|
Windows Registry |
CVE-2021-27091 |
RPC Endpoint Mapper Service Elevation of Privilege Vulnerability |
Important |
3/5 - There are some specific operating systems in the CVSS, so worth a review to see if this effects you. It tends to be older operating systems but does relate to Registry - which is important. |
|
Windows Remote Procedure Call Runtime |
CVE-2021-28336 |
Remote Procedure Call Runtime Remote Code Execution Vulnerability |
Critical |
4/5 - Although flagged as exploitation less likely, these CVE's require network access and a low privilege account, which would be why the critical severity has been assigned. This is once again in the monthly rollout of patchings and available in cumulative or monthly updates for April 2021 |
|
Windows Remote Procedure Call Runtime |
CVE-2021-28434 |
Remote Procedure Call Runtime Remote Code Execution Vulnerability |
Important |
4/5 - These complement the patches mentioned above, they all resolve parts of the same issues stated above, however these are flagged as important rather than critical and once again found in the April 2021 patches. |
|
Windows Resource Manager |
CVE-2021-28320 |
Windows Resource Manager PSM Service Extension Elevation of Privilege Vulnerability |
Important |
3/5 - Applicable to later operating systems (Windows 10 and later versions of Server - 2016 onwards) Once again, this is in your monthly patches for April 2021. |
|
Windows Secure Kernel Mode |
CVE-2021-27090 |
Windows Secure Kernel Mode Elevation of Privilege Vulnerability |
Important |
3/5 - The exploitation is known to be easy. Local access is required to approach this attack. A simple authentication is needed for exploitation. |
|
Windows Services and Controller App |
CVE-2021-27086 |
Windows Services and Controller App Elevation of Privilege Vulnerability |
Important |
3/5 - The exploitation is known to be easy. Local access is required to approach this attack. A simple authentication is needed for exploitation. |
|
Windows SMB Server |
CVE-2021-28325 |
Windows SMB Information Disclosure Vulnerability |
Important |
2/5 - This issue affects an unknown code block of the component SMB. The manipulation with an unknown input leads to an information disclosure vulnerability |
|
Windows TCP/IP |
CVE-2021-28439 |
Windows TCP/IP Information Disclosure Vulnerability |
Important |
3/5 - Affected by this issue is an unknown functionality of the component TCP/IP Driver. The manipulation with an unknown input leads to a denial of service vulnerability. |
|
Windows Win32K |
CVE-2021-27072 |
Win32k Elevation of Privilege Vulnerability |
Important |
3/5 - The exploitability is told to be difficult. Local access is required to approach this attack. The successful exploitation needs an authentication. The technical details are unknown and an exploit is not available. |
|
Windows WLAN Auto Config Service |
CVE-2021-28316 |
Windows WLAN AutoConfig Service Security Feature Bypass Vulnerability |
Important |
3/5 - Difficult to exploit. The manipulation with an unknown input leads to an information disclosure vulnerability via the WLAN AutoConfig Service. |
Hope this table with helpful!

About the Author: Lizzie Arcari
Lizzie joined Foundation IT in 2019 after graduating from University. She is excited to develop her career in the IT industry, learning from the best.